November 08, 2018Swati Khandelwal
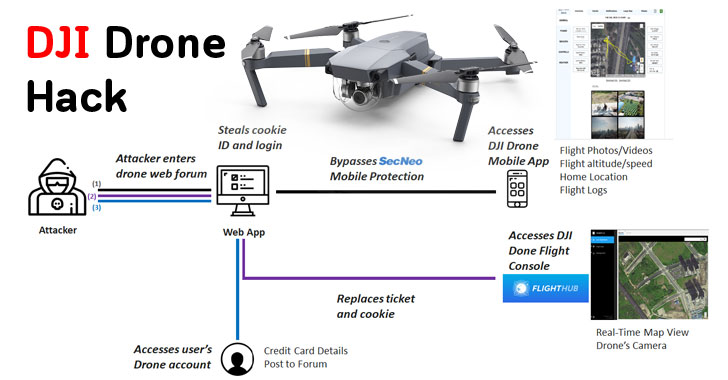
Cybersecurity researchers at Check Point today revealed details of a potential dangerous vulnerability in DJI Drone web app that could have allowed attackers access user accounts and synced sensitive information within it, including flight records, location, live video camera feed, and photos taken during a flight.
Thought the vulnerability was discovered and responsibly reported by the security firm Check Point to the DJI security team in March this year, the popular China-based drone manufacturing company fixed the issue after almost six months in September.
ATTENTION: Click Here To Get Over $100,000 Money Transfer Through Bank Transfer Hackers!!!
ATTENTION: Get Your Hacked Western Union MTCN Transfer and Cash Out Over $2500 within minutes!!!
ATTENTION: Click Here For Your Blank/Cloned ATM Cards for ATM Cashout and Online Purchase!!!
The account takeover attack takes advantage of a total of three vulnerabilities in the DJI infrastructure, including a Secure Cookie bug in the DJI identification process, a cross-site scripting (XSS) flaw in its Forum and a SSL Pinning issue in its mobile app.
The first vulnerability, i.e. not having the “secure” and “httponly”
cookie flag enabled, allowed attackers to steal login cookies of a user
by injecting a malicious JavaScript into the DJI Forum website using the
XSS vulnerability.
“To trigger this XSS attack all the attacker need do is to write a simple post in the DJI forum which would contain the link to the payload,” the researchers explained in a report published today.
“A user who logged into DJI Forum, then clicked a specially-planted malicious link, could have had his or her login credentials stolen to allow access to other DJI online assets,”
Once captured, the login cookies, which include authentication tokens,
can then be re-used to take complete control over the user’s DJI Web
Account, the DJI GO/4/pilot Mobile Applications and account on its
centralized drone operations management platform called DJI Flighthub.
However, to access the compromised account on the DJI mobile apps,
attackers have to first intercept the Mobile application traffic after
bypassing its implementation of SSL pinning by performing
man-in-the-middle (MitM) attack to the DJI server using Burp Suite.
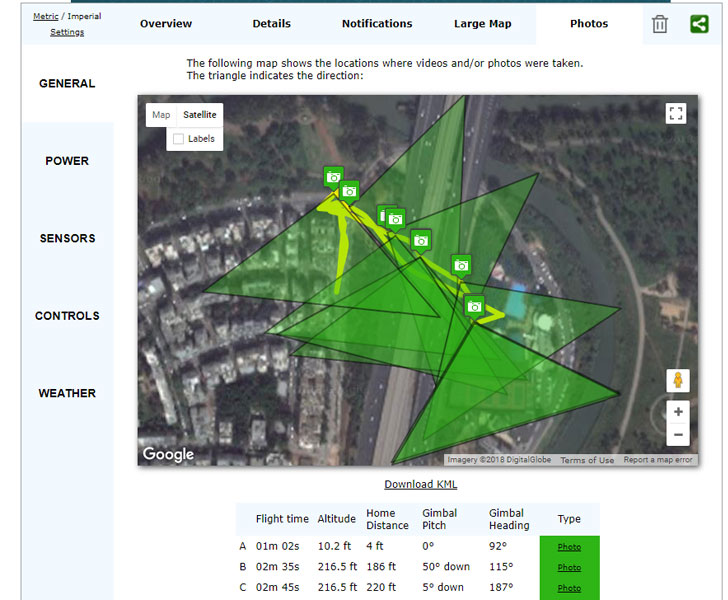
“We also carried out further research and found that by parsing flight logs files we can get much more information such as location and angle of every picture taken during the drone’s flight, the drone’s home location, last known location and more,” researchers said.
DJI classified the vulnerability as “high risk—low probability,” because
successful exploitation of the flaw required a user “to be logged into
their DJI account while clicking on a specially-planted malicious link
in the DJI Forum.”
DJI also said the company did not find any evidence of the flaw being exploited in the wild.
Check Point researchers reported the vulnerability to the DJI through
its bug bounty program, but declined to reveal the financial reward
offered to them. The DJI bug bounty program offers up to $30,000 in
rewards for single vulnerabilities.
DJI has been facing scrutiny in the United States after the Department
of Homeland Security (DHS) released a memo late last year accusing the company of sending sensitive information about the U.S. infrastructure to China through its commercial drones and software.
However, the drone maker denied the allegations, saying that the memo
from the US government office was based on “clearly false and misleading
claims.”