September 10, 2018Swati Khandelwal
Zerodium, the infamous exploit vendor that earlier this year offered $1 million for submitting a zero-day exploit for Tor Browser,
today publicly revealed a critical zero-day flaw in the anonymous
browsing software that could reveal your identity to the sites you
visit.
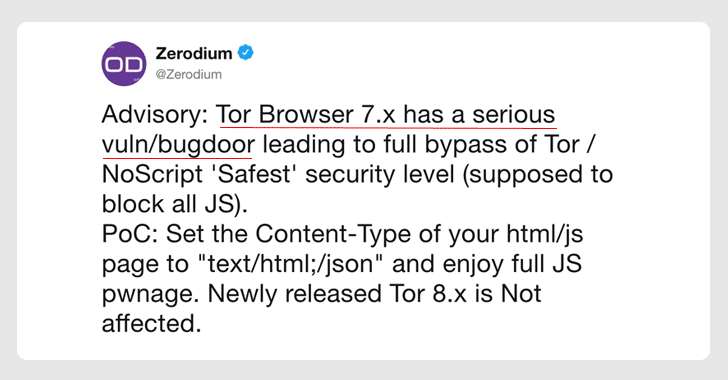
In a Tweet, Zerodium shared a zero-day vulnerability that resides in the NoScript browser plugin
comes pre-installed with the Mozilla Firefox bundled in the Tor
software.
NoScript is a free browser extension that blocks malicious JavaScript,
Java, Flash and other potentially dangerous content on all web pages by
default, though users can whitelist sites they trust.
According to Zerodium, NoScript “Classic” versions 5.0.4 to
5.1.8.6–with ‘Safest’ security level enabled–included in Tor Browser
7.5.6 can be bypassed to run any JavaScript file by changing its
content-type header to JSON format.
In other words, a website can exploit this vulnerability to execute
malicious JavaScript on victims’ Tor browsers to effectively identify
their real IP address.
It should be noted that the latest version of Tor browser, i.e., Tor
8.0, is not vulnerable to this flaw, as the NoScript plugin designed for
the newer version of Firefox (“Quantum”) is based upon a different API
format.
Therefore, Tor 7.x users are highly recommended to immediately update their browser to the latest Tor 8.0 release.
NoScript has also fixed the zero-day flaw with the release of NoScript “Classic” version 5.1.8.7.